Securing the Chain: 3 Basic Considerations for Cyber-Supply Chain Risk Management (C-SCRM) in the Military
Hey there, friends and partners in the defense community!
At Stormcloud Security, we’re all about making cybersecurity approachable, practical, and—most importantly—effective for the folks who protect our nation every day. That’s why we’re thrilled to kick off a brand-new blog series focused on Cyber-Supply Chain Risk Management (C-SCRM) as it applies to military operations and programs.
C-SCRM isn’t just another acronym—it’s the process of identifying, assessing, and mitigating cybersecurity risks that can creep into the hardware, software, and services we rely on throughout the entire supply chain lifecycle (think design, acquisition, deployment, maintenance, and even disposal). For the military, these risks carry extra weight because a single weak link could impact mission assurance, warfighter safety, or national security. The good news? You don’t need a classified briefing to get started with solid fundamentals.
Today we’re keeping it high-level and unclassified with three basic considerations to help military teams build a strong C-SCRM foundation. Over the next few days, we’ll dive deep into each one—sharing real-world examples, actionable tips, and how Stormcloud Security supports implementation. Think of this as your friendly starting point!
1. Know Your Suppliers Inside and Out (Supplier Vetting & Due Diligence)
Every supply chain starts with people and organizations you trust to deliver critical components. The first basic consideration is making sure those partners are vetted rigorously for cybersecurity maturity. This means going beyond the standard “they seem legit” check to evaluate their security practices, compliance (like CMMC levels where applicable), performance history, and potential foreign ownership or influence risks.
Why it matters for the military: Adversaries love targeting less-scrutinized vendors to slip in malware, counterfeits, or backdoors. A strong vetting process helps Program Managers and acquisition teams spot red flags early using tools like the Supplier Performance Risk System (SPRS) and build trusted relationships from day one.
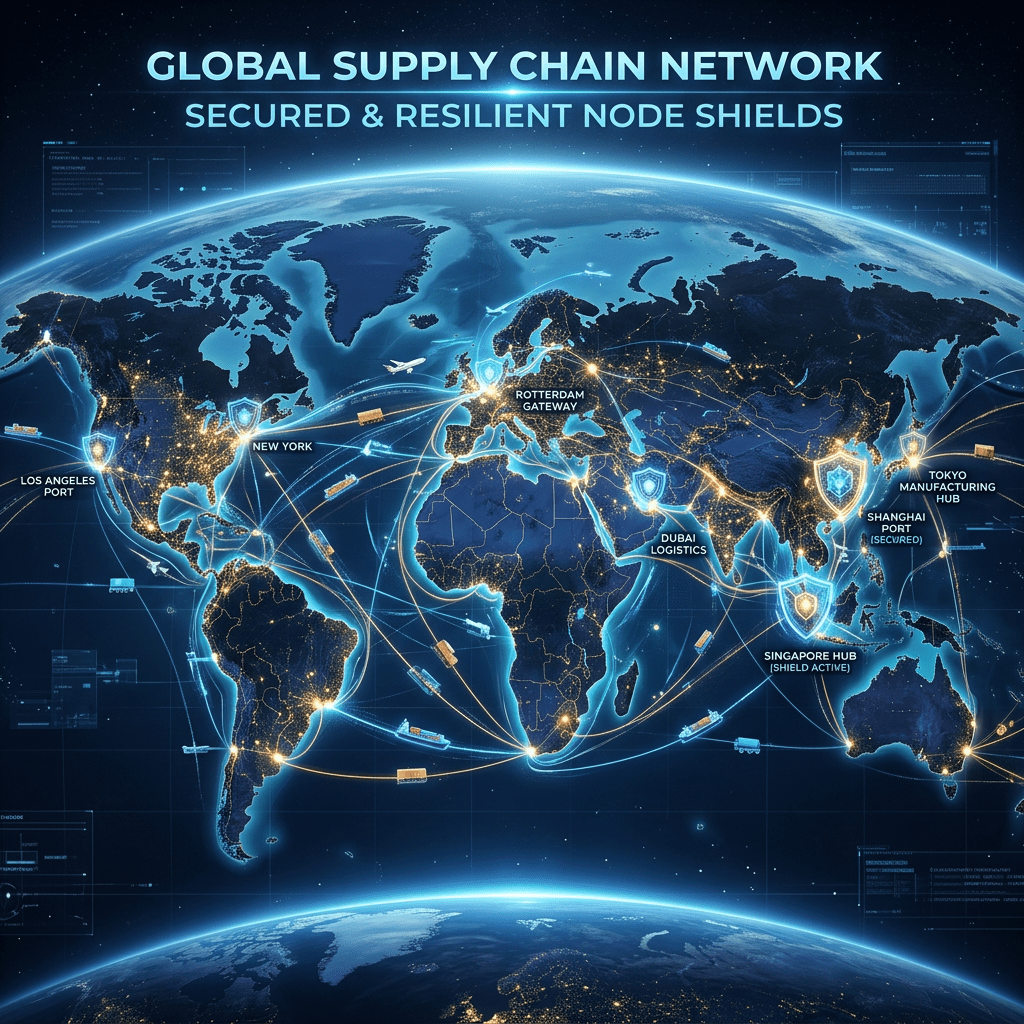
2. Map the Full Supply Chain for Real Visibility
You can’t protect what you can’t see. Consideration number two is gaining clear visibility into every tier of your supply chain—not just your direct vendors, but their sub-suppliers and the origins of hardware, firmware, and software.
In military programs this often ties directly into Program Protection Plans (PPP) and lifecycle risk management. Simple mapping exercises can reveal “key terrain” where a compromise might create an attack path to mission-critical systems. The goal is transparency so you can prioritize high-impact areas and avoid nasty surprises down the road.
3. Integrate C-SCRM into Everyday Risk Management & Build Resilience
C-SCRM isn’t a one-and-done checklist—it’s part of your broader risk framework. The third basic consideration is weaving supply chain risk practices into ongoing identification, assessment, mitigation, and monitoring activities. This includes setting clear contractual cybersecurity requirements, planning for residual risk, and having response playbooks ready if something does go wrong.
For military teams, this means aligning C-SCRM with existing processes like the Risk Management Framework so protections scale with mission needs and evolve as threats change. The payoff? Greater resilience, fewer disruptions, and confidence that your systems can withstand supply-chain-targeted attacks.
These three considerations form the bedrock of a practical C-SCRM program—straightforward, organization-wide, and directly supportive of DoD priorities without needing any special clearances to discuss.
We’ll expand on each one in the coming days with deeper insights, checklists, and how Stormcloud Security’s team can help your program put them into action (from assessments to tailored training and monitoring solutions). If you’re a military program office, acquisition professional, or defense contractor working on these challenges, we’d love to chat.
Drop us a line at Stormcloud Security or connect with us on X @cybercatvoodoo—we’re here to help keep the chain strong so our warfighters can focus on the mission.
Stay secure,
Andrea@StormCloudSec.com 𓃦
Leave a comment